The Foundation: What Are Electronic Access Controls and Why Do They Matter for E-Commerce?
At its core, an electronic access control (EAC) system is a sophisticated method of restricting or permitting entry to a building, area, or resource based on predefined rules and credentials. Unlike traditional mechanical locks, which rely on a physical key for each door, EAC systems leverage electronic credentials, readers, and a centralized management system to provide a far more dynamic and secure approach to access management. Think of it as a digital gatekeeper, perpetually vigilant and highly configurable, ensuring that only authorized personnel can enter designated zones at specified times.
For e-commerce businesses, the relevance of EAC extends far beyond the simplistic notion of locking a front door. Your operations likely encompass a range of physical spaces:
- Warehouses and Fulfillment Centers: These are the nerve centers of your inventory, housing valuable products that are the lifeblood of your business. Unauthorized access can lead to theft, damage, or disruption of critical logistics.
- Office Spaces: Even if your team is largely remote, you might have a central office for administrative staff, product development, or customer service. These spaces contain sensitive data, hardware, and intellectual property.
- Data Centers/Server Rooms: If you host your own servers or have on-premise IT infrastructure, these areas require the highest level of physical security to protect your digital assets.
- Remote Workstations/Equipment: As remote work becomes standard, securing company-issued laptops, specialized equipment, or even home offices where sensitive business activities occur becomes a nuanced challenge that EAC can help address indirectly through policy and integrated solutions.
The transition from traditional keys to electronic systems offers immediate, tangible benefits. With mechanical keys, a lost or stolen key compromises security until every affected lock is re-keyed – a costly, time-consuming, and disruptive process. With an EAC system, a lost access card or mobile credential can be instantly revoked from a central console, rendering it useless. This immediate response capability is critical for maintaining robust security protocols without operational downtime.
Moreover, electronic access controls contribute significantly to improving overall business performance. By automating access management, you free up valuable time and resources that would otherwise be spent on manual key distribution, tracking, and re-keying. The granular control offered by EAC allows you to define specific access levels for different employees, ensuring, for example, that warehouse staff can only access relevant storage areas, while administrative personnel are restricted to office zones. This not only enhances security but also streamlines workflows by ensuring employees only have access to what they need, reducing potential distractions or unauthorized activities.
Ultimately, embracing electronic access controls is a strategic move for any e-commerce enterprise looking to fortify its physical security posture, optimize operational efficiency, and lay a strong foundation for future growth in an increasingly complex and competitive digital landscape. It’s an investment in peace of mind and operational excellence, directly contributing to your bottom line by mitigating risks and improving productivity.
Key Types of Electronic Access Control Systems for Modern Businesses

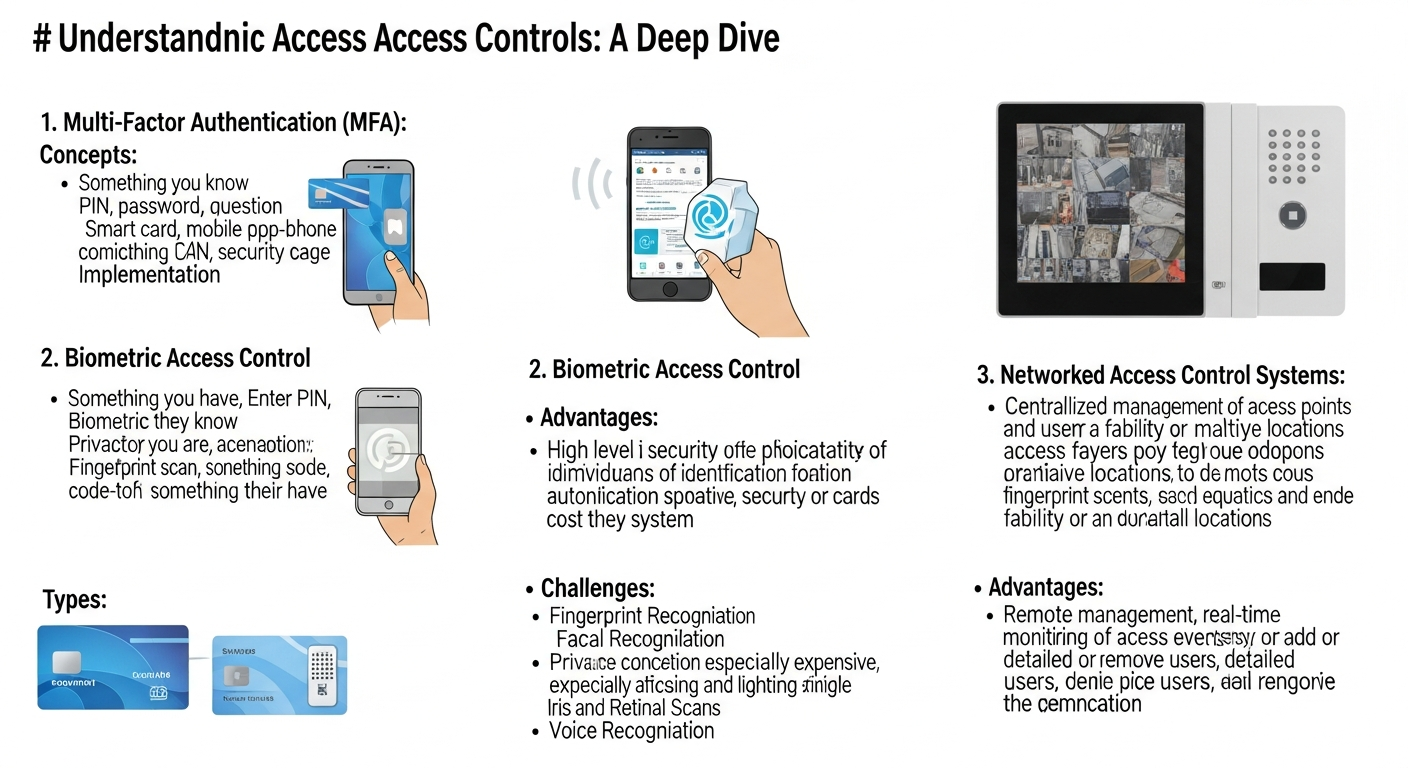
The landscape of electronic access control is diverse, offering a range of technologies to suit different security needs, budgets, and operational complexities. Choosing the right system involves understanding the pros and cons of each type and how they align with your specific e-commerce business environment. Here’s a breakdown of the most prevalent systems:
Proximity Card and Key Fob Systems
These are perhaps the most common forms of EAC. Users are issued physical cards or small key fobs that contain an embedded chip. When the card or fob is held near a reader, it transmits a unique identifier, and if authorized, the door unlocks.
- Pros: Relatively inexpensive, easy to administer, durable credentials, widely adopted.
- Cons: Cards/fobs can be lost, stolen, or “tailgated” (an unauthorized person following an authorized one through an open door).
These systems are ideal for environments with a moderate security risk and a large number of users, such as general office access or warehouse entry points where quick, repeatable access is desired.
Biometric Systems
Biometric access control systems use unique biological characteristics of individuals for identification and authentication.
- Fingerprint Scanners: Users place a finger on a scanner, which reads their unique print pattern.
- Facial Recognition: Cameras scan and match facial features.
- Retinal/Iris Scanners: High-security options that analyze patterns in the eye.
- Pros: Extremely high security as biometrics are difficult to duplicate, eliminate the need for physical credentials (no lost cards), provide irrefutable proof of access.
- Cons: Higher initial cost, potential privacy concerns, can be affected by environmental factors (e.g., dirt on a fingerprint scanner, poor lighting for facial recognition), slower authentication process compared to cards.
Biometric systems are best suited for high-security areas like server rooms, inventory control centers for high-value goods, or research and development labs where intellectual property is paramount. The enhanced security these systems offer can be particularly valuable for manufacturing brands, where protecting designs and prototypes is crucial, aligning with the broader need for robust business insurance to cover such valuable assets.
Keypad/PIN Systems
These systems require users to enter a unique Personal Identification Number (PIN) on a keypad to gain entry.
- Pros: Low cost, no physical credentials needed, simple to install and maintain.
- Cons: PINs can be forgotten, shared, or observed (“shoulder surfing”), requiring frequent changes which can be administratively burdensome. Less secure than card or biometric systems.
Keypad systems are often used for less critical areas, temporary access for visitors, or as a secondary authentication method in a multi-factor setup.
Mobile-Based Access
Leveraging the ubiquity of smartphones, these systems allow users to unlock doors using a dedicated app on their mobile device via Bluetooth, NFC, or Wi-Fi.
- Pros: Highly convenient (most people always have their phone), remote access management, often integrate with other smart building features, can leverage phone’s biometric security (fingerprint/face ID for the app).
- Cons: Dependent on phone battery life, potential for phone theft, requires a smartphone, some users may prefer physical credentials.
Mobile access is gaining traction due to its convenience and potential for seamless integration with other digital tools, making it an attractive option for modern e-commerce businesses with tech-savvy teams.
Cloud-Based vs. On-Premise Systems
Beyond the credential type, EAC systems are also categorized by their infrastructure:
- On-Premise: Software and data are hosted on local servers within your business. Offers maximum control and can be more secure against external cyber threats, but requires significant upfront investment, IT expertise, and maintenance.
- Cloud-Based: Software and data are hosted by a third-party provider in the cloud. Accessed via a web browser or app.
- Pros: Lower upfront costs, scalable, remote management capabilities, automatic updates, reduced IT burden.
- Cons: Relies on internet connectivity, potential data privacy concerns (though reputable providers offer robust security), ongoing subscription fees.
For many e-commerce businesses, especially those with multiple locations or a lean IT team, cloud-based systems offer unparalleled flexibility and scalability, aligning well with the agile nature of online business operations. They exemplify how tech can improve business performance by simplifying management and providing advanced features without heavy infrastructure investment.
Many businesses opt for hybrid solutions, combining different credential types and infrastructure approaches to achieve a layered security strategy that addresses specific risks and operational requirements across their various facilities.
Beyond the Door: Advanced Features and Benefits for E-Commerce Operations
Modern electronic access control systems offer far more than simple door unlocking. They are sophisticated security platforms that, when fully leveraged, can significantly enhance operational efficiency, security posture, and compliance for e-commerce businesses. These advanced features provide invaluable insights and capabilities that traditional lock-and-key systems simply cannot match.
Audit Trails and Reporting
One of the most powerful features of EAC systems is their ability to generate detailed audit trails. Every access attempt – successful or denied – is logged with a timestamp, user ID, and door location. This creates a comprehensive record of who entered where and when.
- Benefit: Invaluable for incident investigation (e.g., if inventory goes missing, you can quickly identify who had access to that area). Essential for compliance with various industry regulations that require documented access control measures. Provides data for optimizing staffing levels and identifying high-traffic areas.
Remote Management and Scalability
Cloud-based EAC systems, in particular, empower businesses with unparalleled remote management capabilities. Administrators can add or revoke access, modify schedules, and view activity logs from anywhere with an internet connection.
- Benefit: For growing e-commerce businesses with multiple warehouses, offices, or remote teams, this centralized control is crucial. It simplifies managing access across geographically dispersed locations, making it easy to onboard new employees, manage vendor access, or restrict access for departing staff almost instantly, regardless of physical presence. This scalability is a prime example of how tech helps improve business performance by streamlining administrative tasks.
Integration with Other Business Systems
The true power of modern EAC lies in its ability to integrate with other critical business systems, creating a holistic security and operational ecosystem.
- Human Resources (HR) Software: Automatically provision or de-provision access based on employee status.
- Time & Attendance Systems: Use access events to track employee work hours accurately, reducing manual errors and improving payroll efficiency.
- Video Surveillance (CCTV): Link access events to video footage, providing visual verification of who entered an area and what they did. This creates an undeniable record, significantly aiding security investigations.
- Alarm Systems: Automatically arm/disarm alarms based on authorized entry/exit, reducing false alarms and ensuring premises are secured.
- Inventory Management Systems: In high-value inventory zones, integrate EAC to log access alongside inventory movements, creating an additional layer of accountability and loss prevention.
Such integrations transform EAC from a standalone security tool into an integral part of your overall business intelligence and operational framework.
Granular Control and Time-Based Access
EAC systems allow for highly granular control over who can access which areas and precisely when.
- Benefit: You can define specific access groups (e.g., “Warehouse Team,” “Admin Staff,” “IT Support”) and assign them different permissions. You can also implement time-based access schedules, ensuring, for instance, that cleaning staff can only enter certain areas between 6 PM and 8 PM, or that contractors have access only for the duration of their project. This level of control significantly enhances security and operational precision, minimizing opportunities for unauthorized access outside of designated hours or roles.
Enhanced Security and Loss Prevention
Beyond simply locking doors, EAC systems actively contribute to loss prevention and overall security.
- Deterrence: The mere presence of a sophisticated EAC system acts as a deterrent to potential intruders or internal theft.
- Rapid Response: Real-time alerts for forced entries or propped doors allow for immediate security response.
- Asset Protection: For businesses that store physical inventory, specialized equipment, or sensitive documents, robust EAC is critical. It directly protects your assets, reducing the likelihood of theft or damage. This directly correlates with why manufacturing brands need business insurance – strong access control reduces risk, potentially leading to lower premiums or easier claims processing in the event of an incident, as you can demonstrate due diligence in security measures. Protecting physical assets is as vital as securing your online storefront.
By moving beyond the basic function of physical entry control, electronic access control systems provide a comprehensive suite of features that empower e-commerce businesses to operate more securely, efficiently, and intelligently. They are an indispensable tool for managing risk, optimizing workflows, and ensuring the long-term viability of your online enterprise.
Implementing EAC: A Strategic Approach for E-ComProfits
Implementing an electronic access control system is a strategic investment that requires careful planning and execution. For e-commerce entrepreneurs, approaching this process methodically will ensure you select a system that not only meets your current security needs but also scales with your business growth and delivers a solid return on investment.
Assessing Your Needs: Identifying Critical Assets and Vulnerabilities
Before looking at any specific system, conduct a thorough security assessment of your business.
- Identify Critical Areas: Which physical spaces house your most valuable assets (inventory, servers, sensitive documents, expensive equipment)? These are your high-priority zones.
- Map Access Points: List all entry and exit points in your facilities – doors, gates, loading docks, server room entrances.
- Understand User Groups: Who needs access to which areas? Employees, contractors, cleaning staff, delivery personnel? What are their typical hours of access?
- Evaluate Current Security: What are the weaknesses of your existing mechanical lock system? Where are the vulnerabilities?
- Consider Future Growth: Do you anticipate opening new warehouses or offices by 2026? Will your team expand significantly?
This initial assessment forms the blueprint for your EAC requirements, helping you define the scope and necessary features of your chosen system.
Budgeting and ROI: A Smart Investment
Electronic access control systems represent a significant investment, but one with clear long-term benefits. When budgeting, consider:
- Upfront Costs: Hardware (readers, controllers, locks), software licenses, installation.
- Ongoing Costs: Maintenance, software subscriptions (especially for cloud-based systems), credential replacement, potential network infrastructure upgrades.
To justify the expense, focus on the Return on Investment (ROI):
- Reduced Losses: Preventing theft, damage, and unauthorized access can save substantial amounts in inventory replacement, equipment repair, and legal fees.
- Improved Efficiency: Automated access management reduces administrative overhead. Integration with time & attendance systems can lead to more accurate payroll.
- Enhanced Compliance: Avoiding fines or reputational damage due to security breaches.
- Lower Insurance Premiums: A robust security system can sometimes lead to reduced business insurance premiums, particularly for manufacturing brands or businesses holding high-value inventory.
- Peace of Mind: Quantifying the value of knowing your assets and data are secure is difficult, but it’s a real benefit that contributes to business stability and owner well-being.
When managing both home and business expenses, it’s crucial to clearly delineate security investments like EAC as a dedicated business expense. These are not personal luxuries but essential operational infrastructure that protects your core business value.
Choosing the Right System: Vendor Evaluation and Feature Matching
With your needs and budget defined, you can now evaluate vendors and systems.
- Feature Alignment: Does the system offer the specific types of credentials (cards, biometrics, mobile), granular control, audit trails, and integration capabilities you require?
- Scalability: Can the system easily expand to accommodate more users, doors, or locations as your business grows?
- Reliability and Support: Research vendor reputation, customer service, and technical support availability. A system is only as good as the support behind it.
- Ease of Use: Is the management software intuitive? Will your team be able to administer it effectively?
- Security Standards: Does the system meet relevant cybersecurity and physical security standards?
- Cloud vs. On-Premise: Revisit this decision based on your IT capabilities, budget, and preference for control vs. convenience.
Installation and Integration: Professional Expertise is Key
Unless you have in-house security experts, professional installation is highly recommended.
- Wiring and Hardware: Proper installation of readers, controllers, and electronic locks is critical for system reliability and security.
- Network Configuration: Ensuring secure and stable network connectivity for your EAC system is paramount, especially for cloud-based solutions.
- System Integration: If you plan to integrate with HR, CCTV, or other systems, ensure the installer has experience with these integrations to avoid compatibility issues.
- Thorough Testing: After installation, conduct extensive testing of all access points and features to ensure everything functions as expected before going live.
Training and Policy Development
A sophisticated EAC system is only effective if your team knows how to use it and adheres to security protocols.
- User Training: Educate all employees on how to use their credentials, the importance of not sharing them, and reporting lost or stolen items.
- Administrator Training: Ensure key personnel understand how to manage the system, add/remove users, set schedules, and retrieve audit logs.
- Develop Clear Policies: Establish written policies for access control, including procedures for lost credentials, visitor access, emergency overrides, and regular security reviews.
By following this strategic approach, e-commerce businesses can successfully implement an electronic access control system that fortifies their physical security, streamlines operations, and contributes directly to their growth and profitability.
Securing Your Future: Best Practices and Future Trends in Access Control
As the e-commerce landscape continues its rapid evolution, so too must the strategies for securing your business. Electronic access control isn’t a “set it and forget it” solution; it requires ongoing attention to best practices and an awareness of emerging trends to ensure your security posture remains robust and future-proof for 2026 and beyond. Integrating advanced tech into your security strategy is a clear example of how tech can help improve business performance, offering proactive protection and enhanced operational insights.
Regular Audits and Updates
Your security needs evolve, and so should your EAC system.
- Periodic Security Audits: Regularly review your access policies, user permissions, and audit logs. Identify any outdated access rights (e.g., for former employees or contractors), unusual access patterns, or areas where security might be unnecessarily lax or overly restrictive.
- Software and Firmware Updates: Keep your EAC software and hardware firmware up-to-date. These updates often include critical security patches that protect against newly discovered vulnerabilities, as well as performance enhancements and new features.
- Hardware Maintenance: Regularly inspect readers, locks, and wiring for wear and tear. Proactive maintenance prevents failures and ensures continuous operation.
Multi-Factor Authentication (MFA) for Physical Access
Just as MFA has become standard for digital security, it’s increasingly applied to physical access for high-security areas. This involves requiring two or more forms of verification (e.g., a card and a PIN, or a card and a fingerprint) to gain entry.
- Benefit: Significantly enhances security, as a single compromised credential is not enough to gain access. For critical areas like server rooms or high-value inventory storage, MFA provides an invaluable layer of protection, making it much harder for unauthorized individuals to breach security.
Cybersecurity Integration: Convergence of Physical and Digital Security
The line between physical and digital security is blurring. An advanced EAC system is often network-connected, making it a potential target for cyberattacks.
- Network Segmentation: Isolate your EAC network from your main business network to limit potential lateral movement for attackers.
- Strong Passwords and Encryption: Ensure all components of your EAC system (software, network devices) use strong, unique passwords and encrypt data in transit and at rest.
- Regular Penetration Testing: Include your EAC system in your regular cybersecurity audits and penetration tests to identify and address vulnerabilities.
A holistic security strategy acknowledges that a physical breach can lead to a digital one, and vice-versa. Robust cybersecurity practices for your EAC system are as important as the physical locks themselves.
Compliance and Data Privacy
Depending on your industry and location, you may need to comply with specific regulations regarding access control and data privacy.
- GDPR, CCPA, etc.: If your EAC system uses biometric data or stores personal information, ensure it complies with relevant data privacy laws regarding data collection, storage, and consent.
- Industry Standards: Certain industries (e.g., finance, healthcare, government contractors) have specific physical security requirements. Ensure your EAC system meets these standards and that your audit trails can demonstrate compliance.
AI and Machine Learning in Access Control
The future of access control is increasingly intelligent and predictive.
- Anomaly Detection: AI-powered systems can learn normal access patterns and flag unusual behavior (e.g., someone accessing a warehouse at 3 AM who never does so, or a door being propped open for an unusually long time). This allows for proactive intervention before a security incident escalates.
- Predictive Security: Leveraging data analytics, AI can help predict potential vulnerabilities or peak risk times, allowing businesses to adjust security protocols dynamically.
- Enhanced Biometrics: AI improves the accuracy and speed of facial recognition and other biometric systems, making them more reliable and user-friendly.
By staying vigilant with best practices and embracing these future trends, e-commerce businesses can ensure their electronic access control systems not only protect their current assets but also evolve to meet the security challenges of tomorrow. This proactive approach to leveraging technology for security is a cornerstone of improved business performance and sustained growth.
FAQ: Your Questions About Electronic Access Controls Answered
What is the primary difference between electronic access control and traditional locks?
The primary difference lies in flexibility and management. Traditional locks use physical keys, offering limited control: if a key is lost, the entire lock system might need re-keying. Electronic access control uses digital credentials (cards, fobs, biometrics, mobile apps) managed by a central system, allowing instant revocation of lost credentials, granular access permissions (who, where, when), and detailed audit trails, which traditional locks cannot provide.
Can electronic access control systems integrate with other business technologies?
Absolutely. Modern EAC systems are designed for integration. They can seamlessly connect with time and attendance software, HR platforms, video surveillance systems (CCTV), alarm systems, and even inventory management platforms. This integration creates a more cohesive security and operational ecosystem, improving efficiency and providing a comprehensive view of activities within your business premises.
Is a cloud-based EAC system secure for my e-commerce business?
Yes, reputable cloud-based EAC systems are built with robust security measures, including data encryption, secure servers, and regular security audits. While they rely on internet connectivity, they often offer superior scalability, remote management, and lower IT overhead compared to on-premise solutions. Always choose a vendor with a strong security track record and clear data privacy policies, aligning with how tech can help improve business performance by simplifying infrastructure management.
How does electronic access control help with managing business expenses?
EAC contributes to managing business expenses by reducing losses from theft or damage, which can be significant for e-commerce inventory. It also lowers administrative costs associated with managing physical keys and re-keying locks. Furthermore, robust security can sometimes lead to lower business insurance premiums, especially for manufacturing brands or businesses with high-value assets. It’s a key operational investment, distinct from personal finance, that protects your business’s financial health.
What should I do if an employee loses their access card or mobile credential?
The immediate benefit of EAC is the ability to instantly revoke lost or stolen credentials from your central management system. This renders the lost item useless for gaining access, maintaining your security integrity without requiring physical lock changes. You can then issue a new credential to the employee, ensuring minimal disruption to their work.
How can I ensure my EAC system remains effective in the long term?
To ensure long-term effectiveness, regularly audit your access policies and user permissions, perform routine software and firmware updates for security patches and new features, and conduct physical maintenance on hardware. Consider implementing multi-factor authentication for high-security areas and integrate your EAC with broader cybersecurity practices. Staying informed about future trends like AI-powered anomaly detection will also help you adapt your system to emerging threats and opportunities by 2026.
Recommended Resources
Check out How To Negotiate Bills And Lower Expenses on Fin3go for a deeper dive.
For more on understanding electronic access, see How To Create A Go To Market Strategy on Kacerr.




